New day, new vulnerability to report. That of today affects almost every device in circulation equipped with a Bluetooth module, with the exception of those with the Android operating system. Users in possession of a smartphone or tablet with an iOS platform or a computer based on Windows 10 or MacOS are therefore exposed, but also Apple smartwatches with watchOS technology and wearables like those of the Fitbit brand.
A Bluetooth vulnerability has been discovered
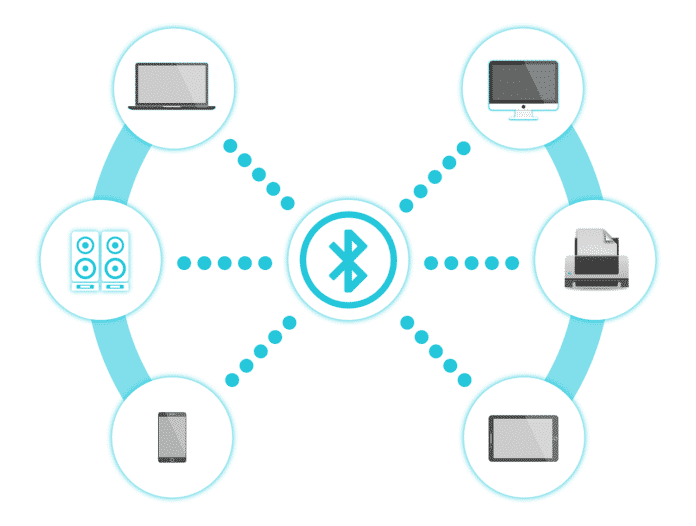
The problem was identified by a team of researchers at Boston University in the BT protocol, more precisely in the implementation of BLE (Bluetooth Low Energy), a specification introduced in 2010 and integrated into all the most recent modules, designed to minimize consumption energy during data transmission.
The vulnerability relies on the method used to connect two devices in the vicinity, passing through unencrypted publicly accessible advertising channels. It allows an attacker with adequate knowledge to spy on the victim by bypassing the protection used by the devices and based on the random generation of MAC addresses, referring to those that the researchers call “identifying token” present in the random string, a parameter considered sufficient to continue to identify a device despite the continuous variation of the MAC address.
With the technique in question it is possible to carry out the tracking of a person, collecting details about his location and other potentially sensitive information. All through a simple algorithm developed ad hoc.
This was discussed at the 19th edition of the Privacy Enhancing Technologies Symposium that took place in Stockholm. Further details can be found in the “Tracking Anonymized Bluetooth Devices” documentation which can be accessed from the link at the end of the article.
Although at the moment there are no breaches based on the described technique to report, considering the expected growth in the number of Bluetooth devices in circulation (from 4.2 billion today to 5.2 billion in 2022), also linked to the increasingly widespread distribution of products linked to the smart home and Internet of Things areas, if such an instrument were to fall into the wrong hands it could be a serious risk to users’ privacy.