Two employees of a US computer security company prove that it is possible to ‘hack‘ the insulin pumps used by diabetics and manipulate the amounts to be dispensed, producing a lethal outcome. They warned of such a possibility in 2018, but nobody paid attention to them. Now they have created a killer app that proves their findings.
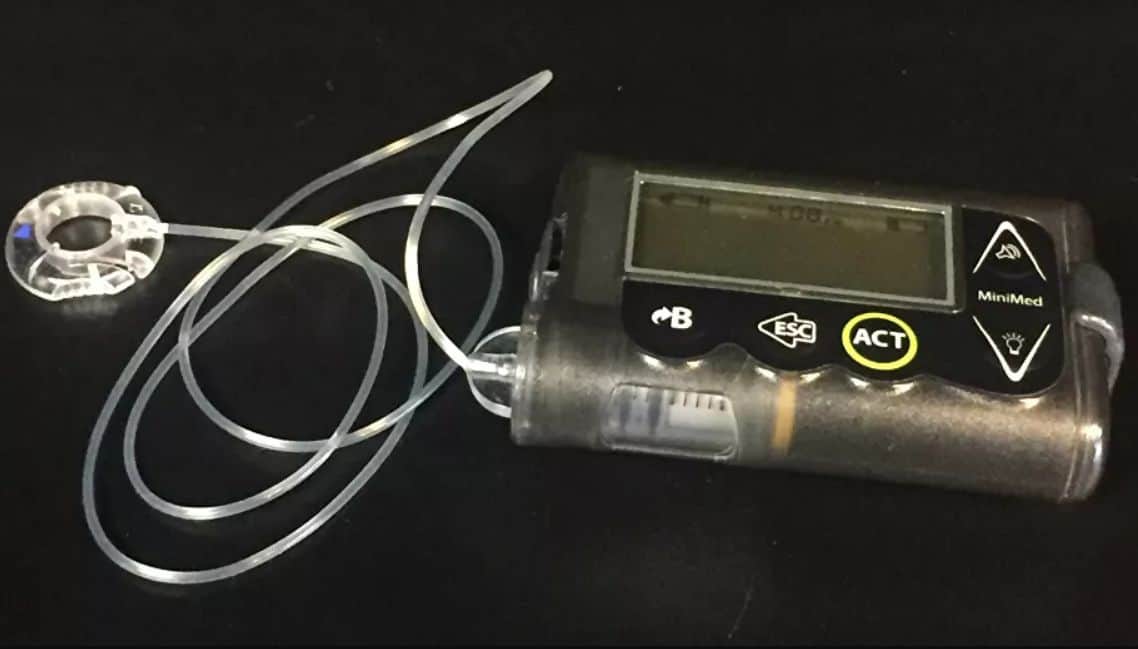
Billy Rios and Jonathan Butts, who work at QED Security Solutions, discovered that the MiniMed and MiniMed Paradigm – Medtronic firm insulin remote-controlled devices – have security flaws and are exposed to remote manipulation.
This was announced during their speech in 2018 at the Black Hat security conference in Las Vegas. Then their conversations with the manufacturer and the US Medicines Agency resulted in practice sterile since they were limited to informing those who could be affected by the contingency. In other words, they did not take measures to resolve the vulnerability of these mechanisms even when they had been informed that the connection between the remote control and the pump that injects insulin automatically was unprotected.
In this way, it was still possible to intercept the signal and release an amount of the hormone other than that previously established, putting the lives of users of this type of device at risk. So Rios and Butts made a drastic decision. “We have simply created a universal remote control for all insulin pumps in the world,” Rios told Wired.
“I don’t know why Medtronic has had to wait for an app that can hurt or kill to take it seriously.”
Pumps
People with diabetes often administer their insulin dose themselves by pressing the necessary buttons on the pumps. But there are some pumps that include remote control, similar to the remote control of a car, thus offering the possibility that health personnel do not have to be on-site to control the process.
What Rios and Butts have found is that it is relatively easy to intercept the frequencies on which the remote control and the bomb carry their connection, since it is not encrypted communication. A hacker could take advantage of open-source programs, accessible to everyone, and program a radio signal to disguise itself as the remote control and send commands that the pump will accept and execute. After making the first contact, a hacker could control that radio signal using a simple smartphone app.
How the app works
And this is exactly what Rios and Butts have done: create an application that also tracks the signals that an insulin pump emits in its environment. They are detected and communicated by the dispenser of this hormone and the app, which replaces the remote control of the pump.
At that moment, a potential user of the application could program a dose different from that needed and with lethal results. The patient could not prevent it, because although the insulin pumps warn with a beep of the administration of the dose, it is done so quickly, that there is hardly any material time to remove the device and prevent the administration of the dose.
Hypothetical attacks can only occur within the range of the remote controls, not from several kilometres. But Rios and Butts claim that with the help of a signal booster, such a radius would be increased by a few meters.
Better late than never
Medtronic and the US regulators admit that there is no way to fix the safety flaws of the affected insulin pump models or to completely disable the remote function.
They first advised patients to manually disable remote access for added protection, but this means depriving themselves of a valuable and potentially life-saving function: one that allows healthcare personnel to dispense treatment by remote control. Thus, Medtronic grants the possibility of replacing these devices with safer ones at no cost. But the climate has become rarefied; it took researchers to take an extreme, even dangerous step to provoke a reaction.