The cybersecurity company SophosLab has made public the existence of an unwanted email campaign that takes advantage of the popularity of the teenage icon Greta Thunberg to spread malware.
The emails linked to this campaign, which has been active since the beginning of the Christmas period, have issues such as “Please help save the planet”, “Greta”, “The greatest demonstration” or “Support Greta Thunberg – Person of the year 2019 according to TIME”.
A wolf in sheep’s clothing
The body of these e-mails encourages the user to join an imminent demonstration … whose time and place do not appear in the text, but in a Word document that in some cases is attached to the mail, and in other cases linked from the same.
The content of these emails is as follows:
“MERRY CHRISTMAS
You can spend Christmas Eve looking for gifts for the children and they will thank you only that day.
Instead, children will thank you all their lives for joining the largest demonstration in protest against government inaction towards the climate crisis.
Support Greta Thunberg – Person of the Year 2019 according to Time magazine.
I invite you to participate. You will find the time and address in the attached file.
SEND this letter to all your colleagues, friends and family. “
Fortunately, those emails that simply link the text file do not use URLs that are currently operational, so nothing happens when users click on them. “The bad thing,” they explain from SophosLab, “is that we can not be sure of what kind of malware they have tried to spread or what may appear in the future in those links.”
In the case of emails that included the attached file, the malware used is Emotet, which was once a Trojan used to steal bank credentials and is currently a sophisticated software used as a gateway for other malicious programs (from other bank Trojans such as QBot even ransomware like BitPaymer).
Once this document is opened, users will see the following legitimate-looking warning message:
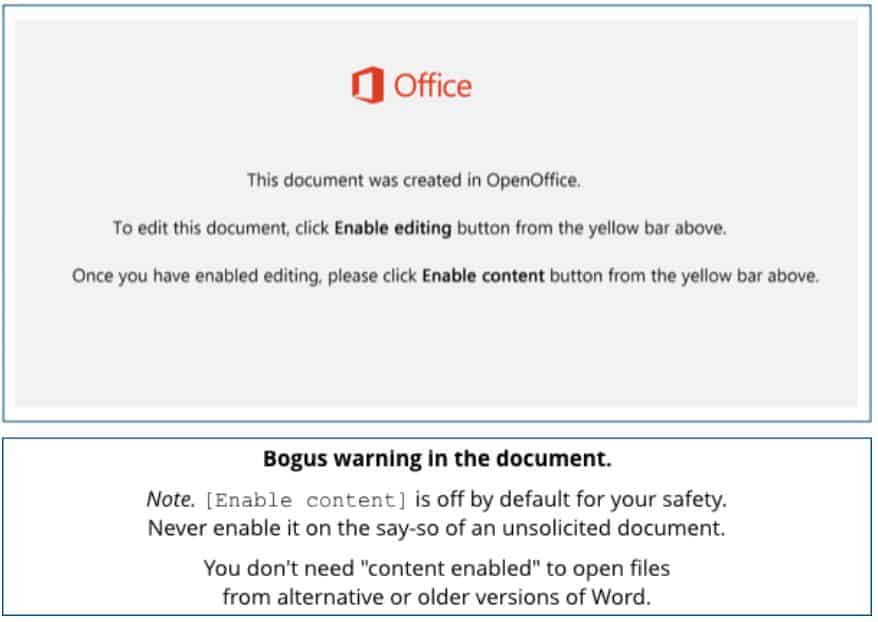
Said message, a mere image inserted in the document, encourages the user to change the default security settings of Word so that it stops blocking the execution of malicious macros. If it was to run, it would connect to the Internet and install Emotet on the computer.
