Trend Micro researchers have discovered a new malware that affects Linux and deals with cryptocurrency mining. In other words, it leverages the computing power of the victim’s computer to generate virtual currency destined for the portfolios of its authors. It has been christened Skidmap and operates in a rather articulated way.
Skidmap, the crypto malware on Linux
As can be seen in the summary scheme attached below, the infection takes place via crontab, a standard Unix system process that deals with managing recurring operations. Subsequently, malicious code is installed that first deactivates some security settings, so that mining can be started without an abnormal use of resources being identified. To make its action go unnoticed as much as possible, Skidmap also alters the statistics relating to CPU usage and network traffic.
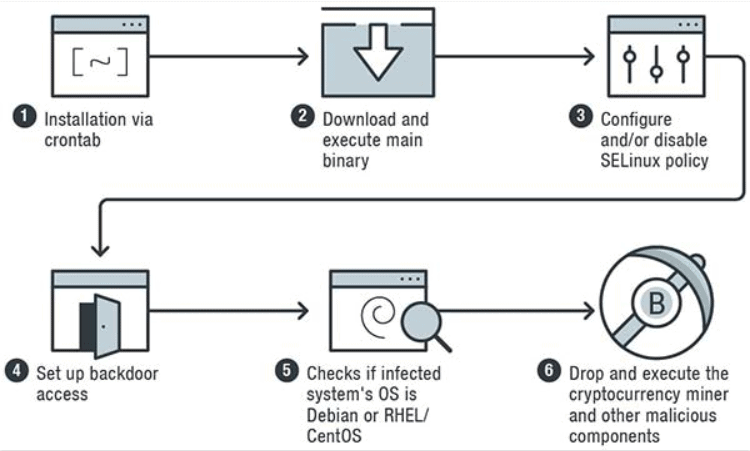
Finally the system file pam_unix.so responsible for authentication with an altered version is replaced, thus providing the authors of the attack the possibility of accessing the machine as if it were one of the legitimately authorized users.
According to Trend Micro, this articulated practice makes Skidmap quite difficult to eradicate, as the malware is designed to install itself again after removal. The advice to stay safe is to keep the terminals up to date. At the moment it is not given to know which cryptocurrency is generated, whether Bitcoin or other.
