For the last four years, a shadowy individual or organization known as ‘KAX17‘ has been joining malicious servers to the Tor network, converting them into nodes at a time when the network is running out of bridges to evade censorship.
And, so far, all evidence point to KAX17’s objective to de-anonymize Tor users, according to cybersecurity experts.
At its peak, KAX17 had up to 900 nodes active and linked to the Tor network, a significant number given that the daily average number of nodes available on Tor is roughly 9,000-10,000.
That is, up to 10% of Tor nodes ended up in the hands of an unknown malicious actor; at the time, there was a 16% probability that a Tor user would connect to the network via one of KAX17’s servers… and a 35% likelihood that their traffic would be routed through one of its mid-nodes.
According to The Record’s analyst Neal Krawetz, this huge presence of servers can be leveraged.
“identify hidden services. It can also be used to decloak users — especially if you have some other means to tracking middle relay past the guard, such as monitoring common public services.”
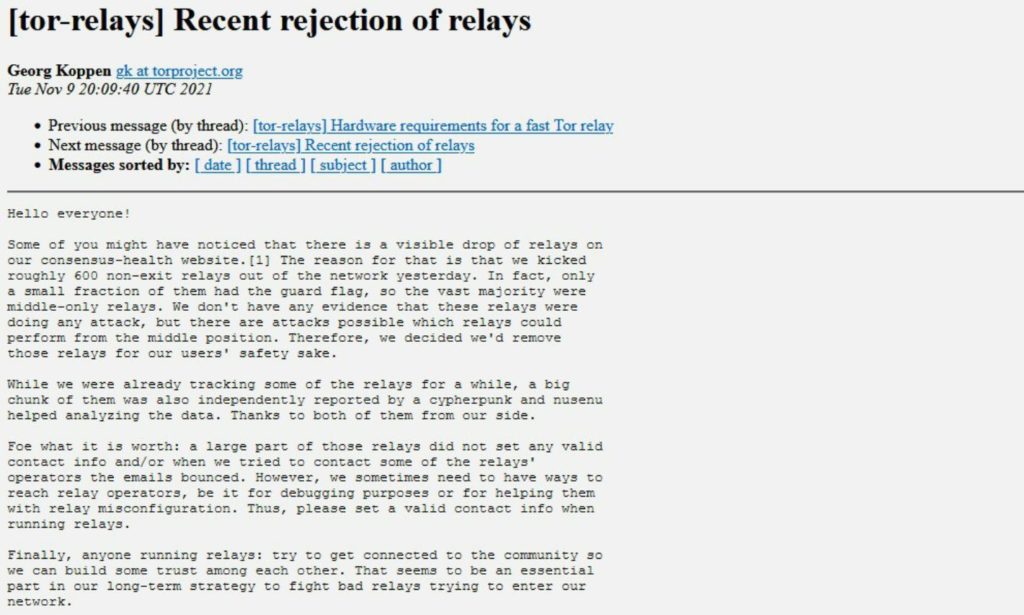
Despite announcing the elimination of all exit nodes in October 2020, Tor project leaders stated a month ago that they had eliminated ‘hundreds of servers’ associated with KAX17 from the network, as a result of cybersecurity researcher ‘Nusenu’ will condemn the resurrection of KAX17 on his blog.
What information do we have about KAX17 and who is behind KAX17?
Neither Nusenu nor the Tor Project wish to speculate on who is behind KAX17: “We are still investigating this attacker,” a Tor Project spokeswoman stated yesterday. The Record media, on the other hand, contends that
“all signs point to a nation-level and well-resourced threat actor who can afford to rent hundreds of high-bandwidth servers across the globe for no financial return.”
Nusenu, on the other hand, says that KAX17 made at least one operational security error, repeating the e-mail address both in the node configuration and when signing up for the Tor mailing list: in the debates, it came to position itself in favor of the suppression of their own servers.
Nusenu has also ruled out the possibility that this hostile individual or actor is the result of a simple scholarly research into ‘Sybil attacks,’ a technique known to be capable of de-anonymizing Tor traffic under specific situations.
Academic researchers, he claims, tend to arrange their work in terms of time constraints (although KAX17 has been active since 2017), they do not quickly replace destroyed nodes with new ones… and, in general, they do not need to resort to strategies like these. because the Tor Project and the research community are usually quite well connected.
Image Credit: Pixabay
You were reading: Someone has been hacking Tor servers to de-anonymize users for four years
