After Elastic released the essential security features of the Elastic Stack for free at the end of May, the next step follows. With the release of Elastic Stack 7.2, the company continues to expand its security offering, providing complete security information and event management (SIEM). In addition to the well-known data collectors such as Auditbeat or Winlogbeat, the format ECS (Elastic Common Schema) introduced at the beginning of the year should help to be able to analyze data across all sources.
Programming Language Julia, an alternative to Python, R and Matlab
Integrated security workflows
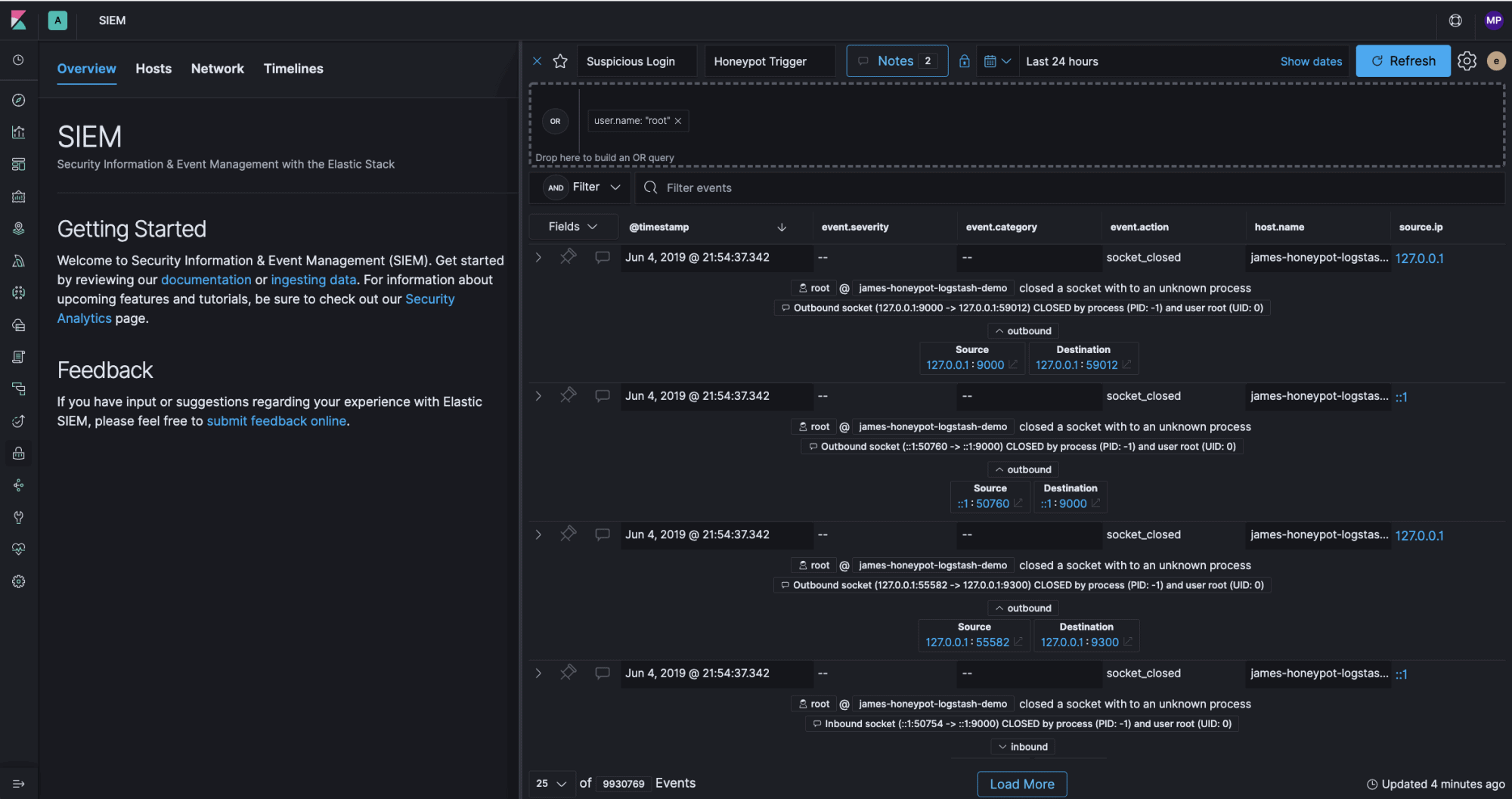
Elastic SIEM is designed as an interactive workspace that allows security teams to analyze events and conduct initial investigations. Kibana’s built-in SIEM app bundles a timeline event viewer with host and network security event analysis, allowing Security Operations Center (SOC) to leverage typical workflows to find potential threats and impending problems. As part of Elastic Stack 7.2, Elastic SIEM is available as beta for free.
An on-premises installable version of the Elastic App Search is now also available to developers free of charge for integration into any application. Like the search application offered by Elastic as a managed service since a year ago, the on-premise version also offers comprehensive configuration options from data ingestion to APIs and UI frameworks to relevance control and analysis of search queries.
Here is Raspberry Pi 4, with 4 GB of RAM and 4K output
Improved observability
Other improvements in Elastic Stack 7.2 mainly concern improvements in observability. Elastic APM now has the first beta version of the long-announced .Net Agent. In addition, the browser-based Real User Monitoring (RUM) agent now also supports single-page applications. A new Metrics Explorer also provides deeper insights into key infrastructure metrics. Especially in cloud-native environments, within the framework of the Kubernet and container monitoring, NATS, CoreDNS and the log format CRI-O can now also be used.
A complete overview of all the improvements in Elastic Stack 7.2 can be found in the blog post for release.
Wine project fears problems with 64-bit Ubuntu
